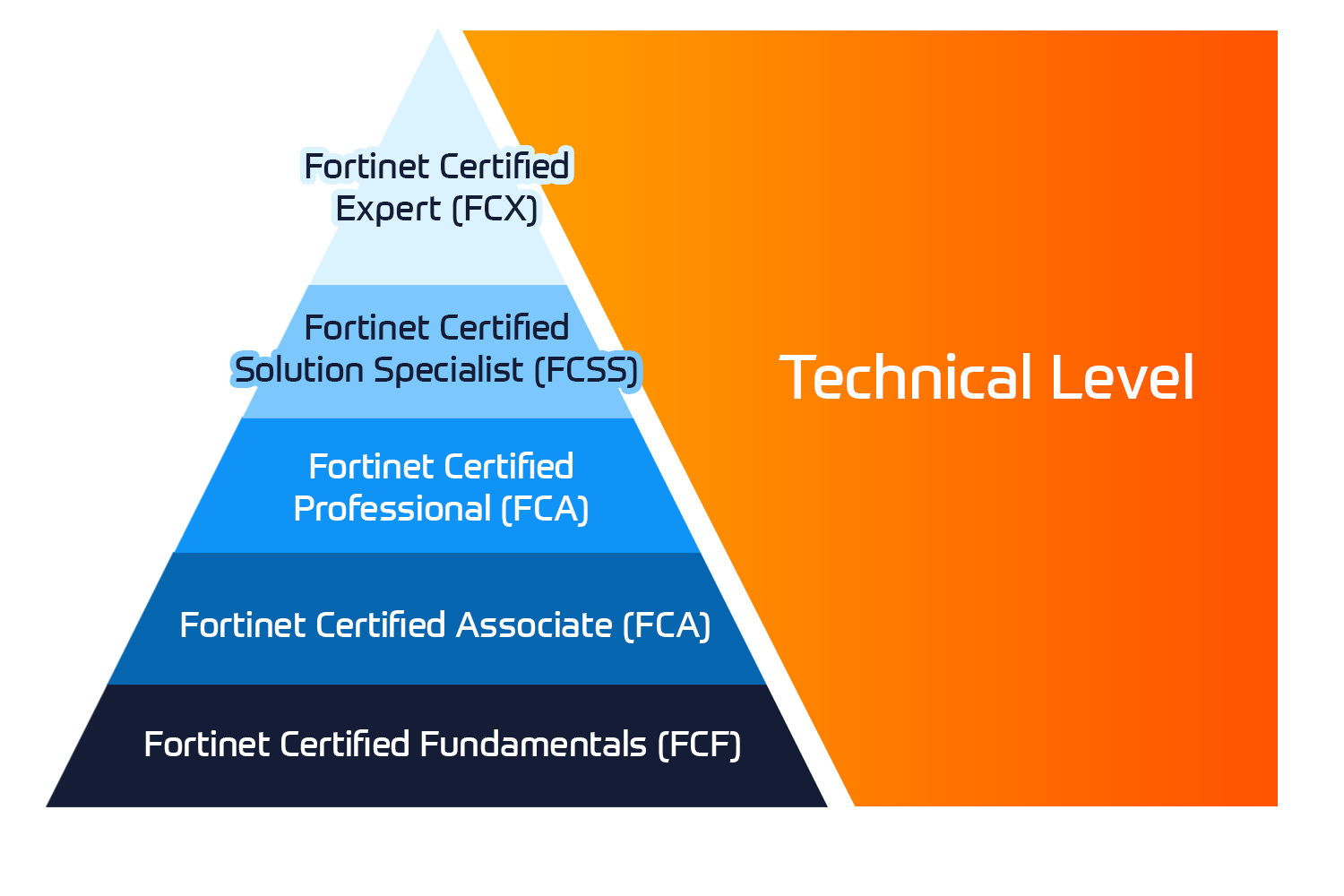
This CompTIA Advanced Security Practitioner (CASP+) training course will prepare you to successfully achieve this in-demand certification and teach you to assess, investigate, examine, and research potential security threats in your organisation.
In this certification training course, you will gain the foundational knowledge to fully prepare for the CASP+ exam (CAS-003). Earning CASP+ certification demonstrates your knowledge and skills in enterprise security, risk management, research and analysis, and the integration of computing, communications, and business disciplines.
Associated Certification:
- Exam Code: CAS-004

 United Kingdom
United Kingdom Germany
Germany Denmark
Denmark Sweden
Sweden Italy
Italy Netherlands
Netherlands Norway
Norway 















 Kesto
Kesto  Toimitus
Toimitus  Hinta
Hinta