In this course, you will learn how to use FortiSIEM in a multi-tenant environment. You will learn about rules and their architecture, how incidents are generated, how baseline calculations are performed, the different methods of remediation available, and how the nested queries and lookup tables work for advanced analytics using FortiSIEM. You will also learn how to integrate FortiSOAR with FortiSIEM.
Product Versions:
- FortiSIEM 6.7.4
- FortiSOAR 7.3.2
- FortiGate 7.2.2
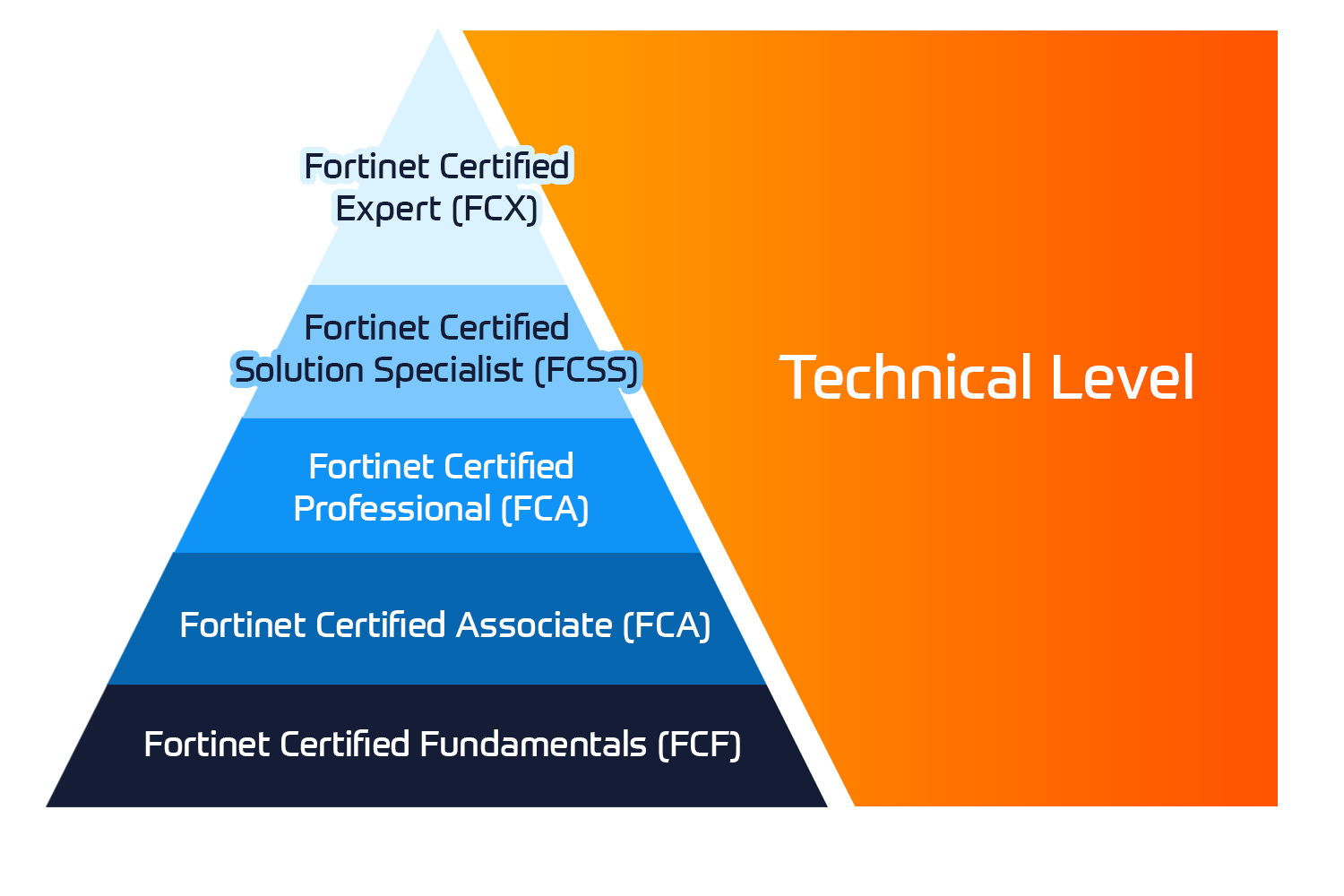
Exam:
- This course prepares you for the Fortinet NSE 7 – Advanced Analytics 6.3 exam.
Associated Certifications:

 United Kingdom
United Kingdom Germany
Germany Denmark
Denmark Sweden
Sweden Italy
Italy Netherlands
Netherlands Norway
Norway 















 Kesto
Kesto  Toimitus
Toimitus  Hinta
Hinta