This five-day course is designed to provide students with the knowledge required to work with Juniper Connected Security devices. This course uses Junos CLI, Security Directory, J-Web, and other Web user interfaces to introduce students to Juniper Connected Security devices. The course provides further instruction on how Juniper Networks approaches a complete security solution for current and future security problems, called Juniper Connected Security.
Key topics include tasks for advanced security policies, application-layer security using the AppSecure suite, intrusion prevention system (IPS) rules and custom attack objects, Security Director management, Juniper Advanced Threat Prevention (ATP) Cloud management, Juniper ATP Appliance management, Juniper Secure Analytics (JSA) management, Policy Enforcer management, Juniper Identity Management Service (JIMS), vSRX and cSRX usage, SSL Proxy configuration, and SRX high availability configuration and troubleshooting.
Through demonstrations and hands-on labs, students will gain experience in configuring and monitoring the Junos OS and monitoring basic device operations. This course is based on Junos OS Release 22.1R2, Junos Space 22.2R1, Security Director 22.2R1, JATP 5.0.6.0, JSA v7.3.2, Policy Enforcer 22.2R1, and JIMS 1.1.5R1.
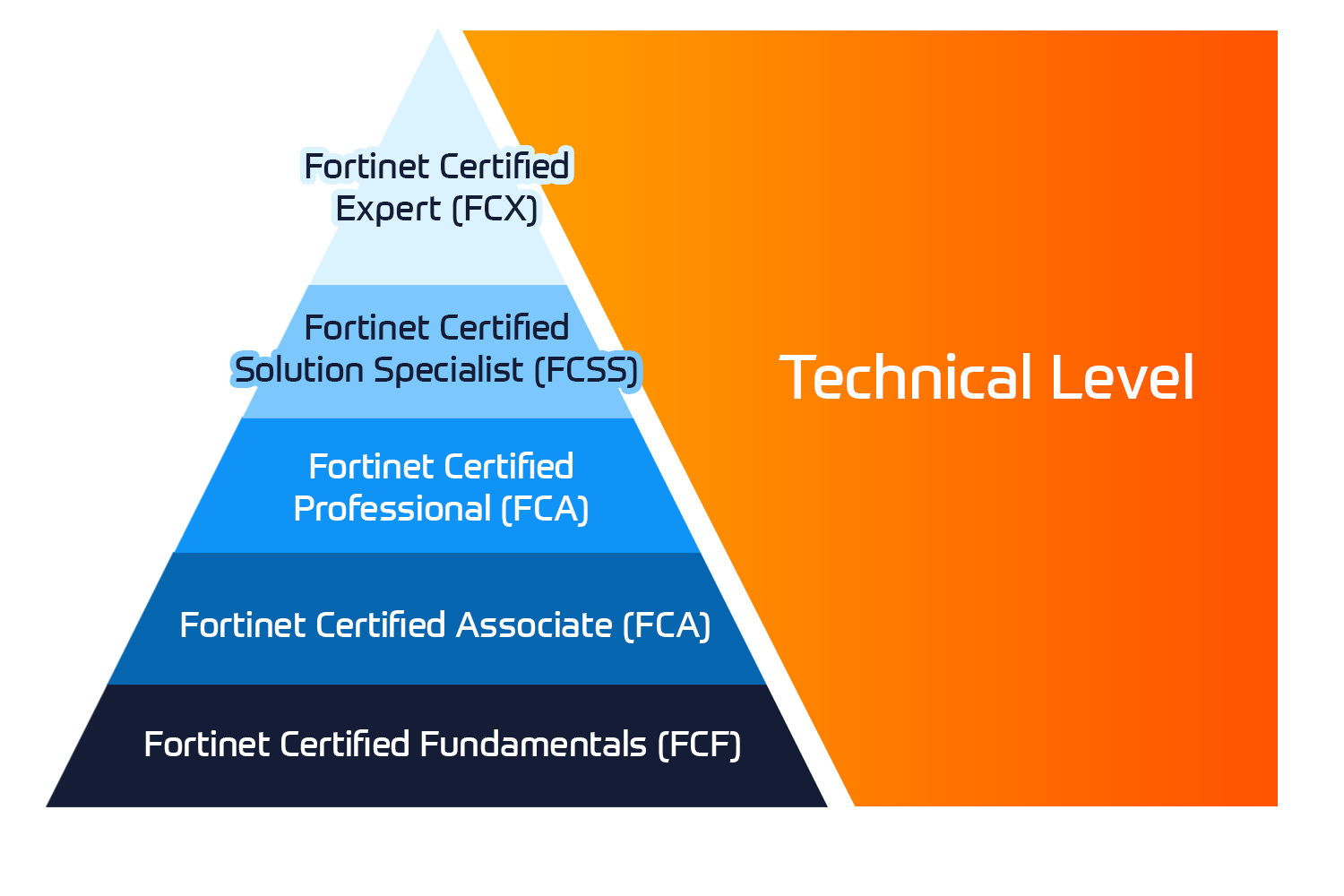
Associated Certification:
Security, Specialist (JNCIS-SEC)

 United Kingdom
United Kingdom Germany
Germany Denmark
Denmark Sweden
Sweden Italy
Italy Netherlands
Netherlands Norway
Norway 















 Kesto
Kesto  Toimitus
Toimitus  Hinta
Hinta