Onko ICT-infrastruktuurisi turvallinen?
Nykypäivän modernissa yritysmaailmassa yrityksen on mahdotonta toimia ilman tietokonejärjestelmään perustuvaa tieto- ja viestintäteknologiaa (ICT). Käytetäänpä järjestelmiä erilaisen materiaalin, erimerkiksi tarjousten tai raporttien, luomiseen tai tietojen analysointiin ja tietokantojen käyttämiseen, kaikilla näillä järjestelmillä on yksi keskeinen tarkoitus: helpottaa päivittäistä liiketoimintaa ja tarjota nopea pääsy vaadittuihin tietoihin.
Internet ja internet-yhteys, niin arkipäiväisiä asioita kuin ovatkin, kätkevät sisälleen useita vaaroja. Vaikka internetin tietoliikenneverkot ovat suunniteltu auttamaan ja parantamaan suorituskykyä, niitä voidaan käyttää työkaluina myös yritykseen kohdistuvaan hakkerointihyökkäykseen.
Valitettavasti internetin vaarat piilevät monella taholla. Klassisten tietokonevirusten ohella vaarallisia ovat erityisesti viime aikoina suositut kryptovirukset, joita käytetään suoraan rahan kiristykseen uhreilta. Tietokonejärjestelmät ovat kaukana täydellisistä ja ohjelmistovirheitä havaitaankin päivittäin. Tällaisten haavoittuvuuksien avulla on mahdollista murtautua järjestelmään ja vaarantaa sen turvallisuus, ellei asiaa korjata nopeasti.
Pelottavinta on se, että hakkerin onnistuessa murtautumaan järjestelmään, voi kestää viikkoja ellei kuukausia ennen kuin tilanne havaitaan ja sitä päästään selvittämään. Tuona aikana hakkeri voi tehdä paljon vahinkoa. Useimmiten vahingot liittyvät tietojen varastamiseen ja/tai muuttamiseen.
Miltä tietokonejärjestelmään murtautumisen (hakkeroinnin) anatomia näyttää?
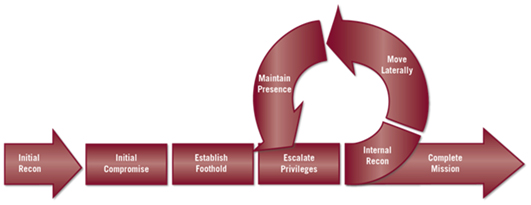
Aluksi hakkeri yrittää saada peruspääsyn tietokonejärjestelmään. Tämä tehdään yleensä analysoimalla käyttäjät (Recon), varastamalla olemassa olevan käyttäjän identiteetti (Initial compromise) ja hankkimalla käyttöoikeudet (establish foothold). Tässä muutamasta päivästä muutamaan viikkoon kestävässä vaiheessa hakkeri saa peruspääsyn tietokonejärjestelmään.
Seuraavassa vaiheessa, joka voi kestää viikkoja tai jopa kuukausia, hakkeri yrittää jo olemassa olevaa käyttöoikeuttaan hyödyntämällä laajentaa oikeuksiaan tai ottaa haltuunsa järjestelmänvalvojan identiteetin (loop escalate privileges, Internal recon, lateral movement, maintain a presence).
Viimeisessä vaiheessa, kun hakkeri on jo hankkinut järjestelmänvalvojan oikeudet, siirtyy se aktiiviseen hyökkäysvaiheeseen, jonka aikana tietoja kopioidaan, muutetaan tai pääsy niihin estetään (lunastuspyynnöllä).
Muissa tapauksissa hakkeri voi yrittää poistaa järjestelmän käytöstä yleensä lähettämällä liian monta pyyntöä, mikä ylikuormittaa järjestelmää ja se saattaa lakata toimimasta. Tämä on niin kutsuttu palvelunestohyökkäys (DoS).
Näistä syistä on melko realistista kysyä: “Onko tietokonejärjestelmäni turvallinen?” Tai ehkä enemmänkin: “Kuinka turvallinen ICT-järjestelmäni on?” ja ennen kaikkea “Kuinka voin suojata itseäni?” Vastaus ei ole helppo, mutta periaatteessa tietokonejärjestelmien suojaaminen uhkilta ja vaaroilta voidaan jakaa kolmeen segmenttiin:
• Käyttäjien koulutus
• Aktiivinen / Reaktiivinen suojaus
• Ennakoiva suojaus
Käyttäjäkoulutuksessa on tärkeää, että käyttäjät oppivat tunnistamaan arjen uhkia ja vaaroja sekä ohittamaan tai poistamaan ne. Tämä on ratkaisevassa asemassa, jotta voidaan vähentää hakkereiden mahdollisuutta saada haltuunsa käyttöoikeudet. Näin mahdolliset hyökkäykset voidaan ehkäistä ajoissa.

Nämä ovat erikoiskoulutuksia, joiden tavoitteena on lisätä käyttäjien tietoisuutta vaaroista ja opettaa käyttäjiä tunnistamaan helposti hyökkäysyritykset. Mitä tulee aktiiviseen ja reaktiiviseen suojaukseen, markkinoilla on useita ratkaisuja, joilla pyritään estämään jo tunnetut hyökkäykset. Tämän segmentin ratkaisuja ovat virustorjuntaohjelmat, palomuurit, roskapostisuodattimet ja vastaavat. Kaikki nämä tuotteet toimivat ennalta määritettyjen ohjelmistomatriisien tai -tyyppien perusteella. Siksi ne kuuluvatkin aktiivisen ja reaktiivisen suojan segmenttiin. Joutuessa viruksen tai muun hyökkäyksen kohteeksi onkin erityisen tärkeää, että koodi syötetään virusluetteloon. Näin se tunnistetaan tulevaisuudessa haitalliseksi koodiksi tai virukseksi. Näistä syistä virustorjuntaohjelmiston määritelmät on päivitettävä säännöllisesti.
Ennakoiva suojaus -segmentti on vähiten tunnettu suojatyyppi, vaikka se on luultavasti juuri tärkein tapa tarkistaa, ovatko ICT-järjestelmät turvallisia.
Ennakoiva suojaus on simulaatio hakkerihyökkäyksestä, joka suoritetaan ICT-järjestelmään, sovellukseen, tietoliikenneverkkoon tai verkkosivustoon, jotta voidaan havaita mahdolliset ohjelmiston haavoittuvuudet ja järjestelmän puutteet ennen kuin haitalliset hakkerit havaitsevat ja/tai käyttävät niitä hyväkseen.
Tämä prosessi, nimeltään “Ethical Hacking”, on riippumaton arvio tietyn ICT-järjestelmän turvallisuudesta.
Lopuksi vastaus kysymykseen “Kuinka suojella itseäni?”. Ainoa oikea vastaus on kaikkien kolmen segmentin yhdistelmä. Käyttäjiä tulisi kouluttaa verkkotoiminnan mahdollisista uhkista ja vaaroista; Järjestelmät tulee varustaa virustorjuntaohjelmistolla ja palomuurilla. Ennen kaikkea koko järjestelmän tulee olla eettisten hakkereiden perusteellisessa valvonnassa, jotta voidaan varmistaa, että kaikki tietoturvajärjestelmän komponentit ovat konfiguroitu oikein ja, että ne suorittavat tehtävänsä.
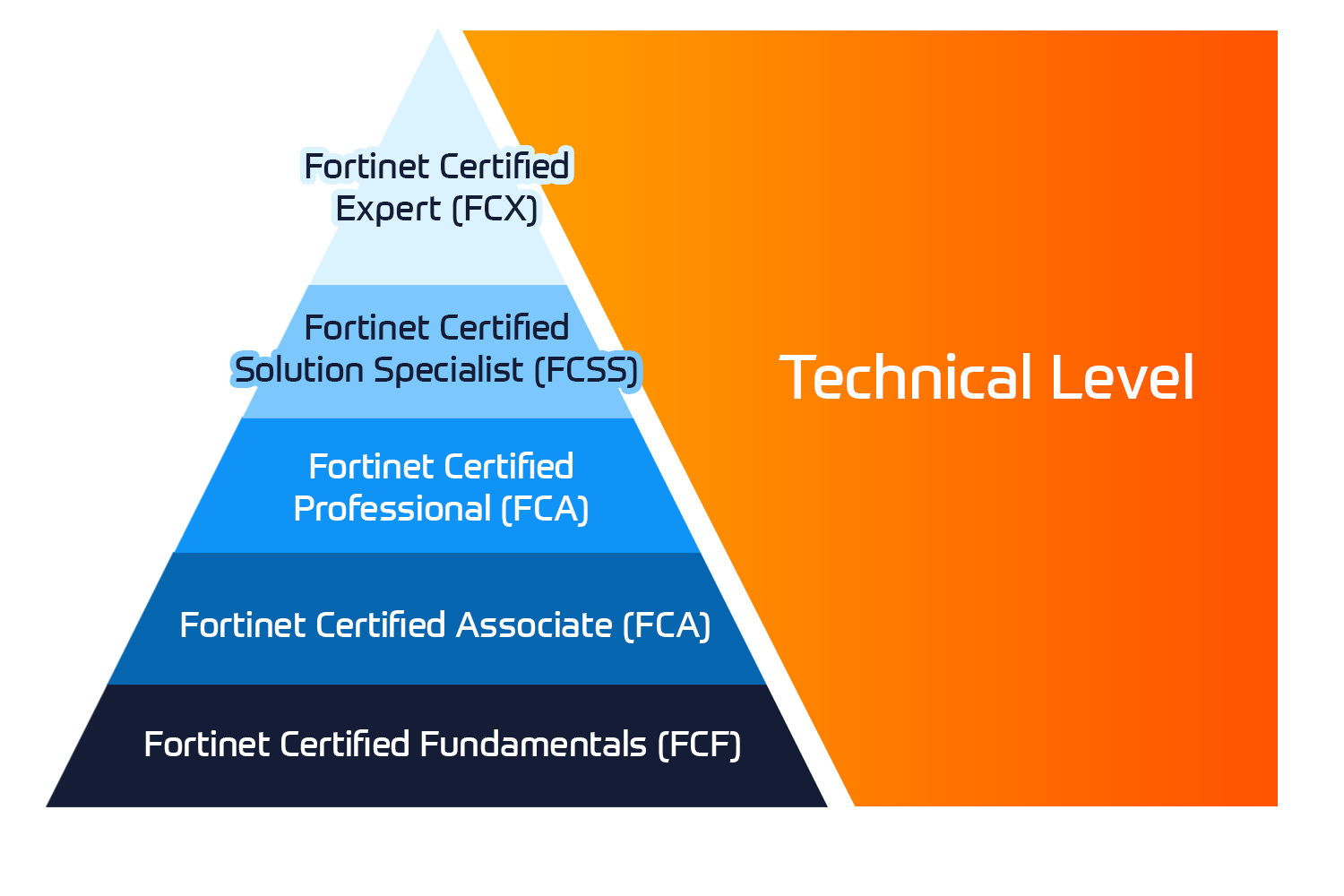
Insoft Services tarjoaa ICT-palveluita ja koulutusta käyttäjille sekä IT-asiantuntijoille.

 United Kingdom
United Kingdom Germany
Germany Denmark
Denmark Sweden
Sweden Italy
Italy Netherlands
Netherlands Norway
Norway 
















No Comments